
Your Enterprise Browser Isnt the Data Leak Risk It Once Was
August 28, 2025
F5 acquires MantisNet to expand cloud-native observability capabilities
September 2, 2025The Good, the Bad and the Ugly in Cybersecurity – Week 35
The Good | Interpol Cracks Down on Cybercrime as U.S.
Sanctions North Korean IT Scheme
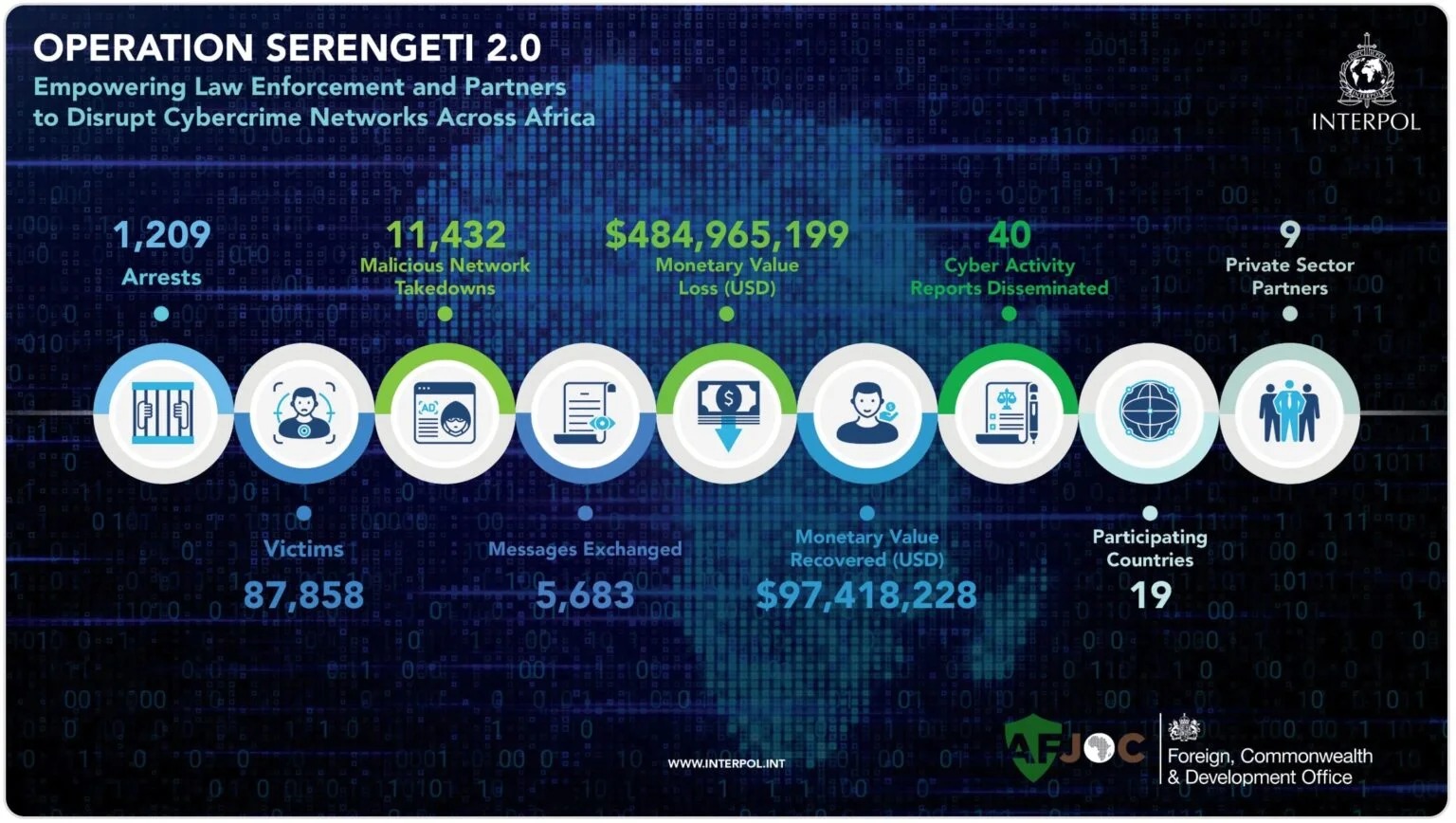
Interpol announced the arrest of over 1200 suspects in
Operation Serengeti 2.0, a three-month crackdown on cybercrime across Africa.
Conducted between June and August, the operation dismantled 11,432 malicious
infrastructures, seized $97.4 million, and disrupted attacks impacting nearly
88,000 victims worldwide. Investigators from 18 African nations and the U.K.
collaborated under the African Joint Operation against Cybercrime,
supported by various private sector partners. Targets included ransomware operators,
online scammers, and business email compromise (BEC) groups.
Group-IB
This is the latest in a series of coordinated operations
across Africa, following earlier successes such as Operation Red Card and
Operation Serengeti (2024). Interpol emphasized that each
initiative strengthens cross-border cooperation, expanding both intelligence sharing
and investigative expertise, which garner larger, more impactful results in the
fight against transnational cybercrime.
The U.S. Treasury’s OFAC has sanctioned two
individuals and two entities tied to North Korea’s illicit remote IT
worker scheme, which funds its weapons and missile programs. Russian
national Vitaliy Sergeyevich Andreyev, North Korean official Kim Ung Sun,
Shenyang Geumpungri Network Technology (China), and Korea Sinjin Trading
Corporation were named for defrauding American businesses. Andreyev allegedly
helped transfer nearly $600,000 in cryptocurrency-to-cash payments, while
Shenyang Geumpungri generated over $1 million in profits since 2021.
The IT worker scheme, specifically, embeds North Korean
IT workers in global companies using fake identities and stolen documents.
Recent investigations indicate a growing reliance on AI tools
to build false resumes, pass interviews, and deliver work. Authorities warn the
operation also enables malware insertion, data theft, and extortion
against targeted firms.
The Bad | UpCrypter Malware Loader Spreads Through Fake
Voicemails to Install RAT Payloads
A new phishing campaign distributing a
malware loader known as UpCrypter is using fake voicemail notifications
and purchase orders as lures. Active since early August 2025, the campaign has
primarily targeted organizations in manufacturing, technology, healthcare,
construction, and retail/hospitality, with infections observed in Austria,
Belarus, Canada, Egypt, India, Pakistan, and several others worldwide.
The attack begins with carefully crafted phishing emails
containing malicious URLs to fraudulent landing pages that mimic corporate
branding by embedding a victim’s domain name and logo. Victims are prompted to
download what appears to be a voicemail or PDF, delivered as a ZIP archive
containing an obfuscated JavaScript file. Once executed, the script checks for
internet connectivity, scans for forensic tools or sandbox environments, and
then retrieves the next-stage malware from an external server.
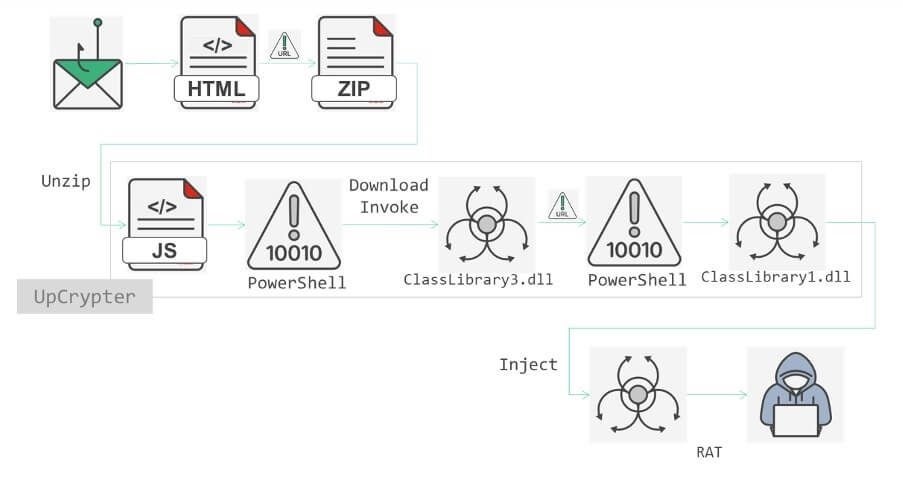
Source: Fortinet
UpCrypter serves as a dropper for multiple remote access tools (RATs), including PureHVNC RAT, DCRat, and Babylon RAT, all of which enable full control of infected systems and provide attackers with remote surveillance, credential theft, and command execution capabilities. Payloads may be delivered in plain text or concealed via steganography inside images. A parallel distribution method uses a Microsoft Intermediate Language (MSIL)-based loader that performs similar anti-analysis checks before fetching an obfuscated PowerShell script, a DLL, and the main payload.
The final execution sequence embeds data from the DLL and payload directly into memory, bypassing the file system to minimize forensic artifacts. Security researchers warn that UpCrypter’s evolving design, combining layered obfuscation, sandbox evasion, and flexible RAT deployment, points to an actively maintained delivery ecosystem capable of persisting across environments that rely only on traditional defenses.
The Ugly | Salt Typhoon Expands Global Cyber-Espionage Campaign via Router Exploits
Authorities from 13 nations, including the U.S., U.K., Canada, Germany, and Japan, have issued a joint security advisory linking three Chinese tech companies to advanced persistent threat (APT) group Salt Typhoon (also tracked as UNC2286). Receiving intelligence services, cyber tools, and stolen data, the China-based actor has been able to intensify its global cyberespionage operations. Targeting has been focused on telecommunications, government, transportation, and military infrastructure since at least 2019.
The group focuses on exploiting backbone, provider edge (PE), and customer edge (CE) routers, using flaws such as CVE-2018-0171, CVE-2023-20198, CVE-2023-20273, CVE-2023-46805, CVE-2024-21887, and CVE-2024-3400. Compromised devices are modified for persistence through generic routing encapsulation (GRE) tunnels, altered Access Control Lists (ACLs), custom containers, and added IP-controlled ports. Attackers further exploit Terminal Access Controller Access Control System Plus (TACACS+) authentication traffic on TCP/49 to harvest highly privileged administrator credentials, enabling lateral movement across network environments.
To date, Salt Typhoon has attacked over 600 organizations across 80 countries. The advisory emphasized that intrusions into telecom and transportation networks have enabled Chinese intelligence services to track communications and movements worldwide. Experts urge defenders to watch for configuration changes, container activity, unusual tunnels, and integrity issues in firmware and logs.
To counter Salt Typhoon and similar threats, the guidance calls for rapid patching, adoption of zero-trust models, disabling unused services, and strengthening authentication. Officials warn that adversaries will only grow more sophisticated, stressing the need to retire outdated systems and harden defenses.
Related Articles
When are attacks truly driven by AI?
February 25, 2026 0
Dell PowerEdge R770 Review A Fluid New 2U Server
February 18, 2026 0Scalar Tape Storage
February 15, 2026 0Why Certification Has Become a Strategic Control for CISOs
February 15, 2026 0


