Domain Controller Hijacking
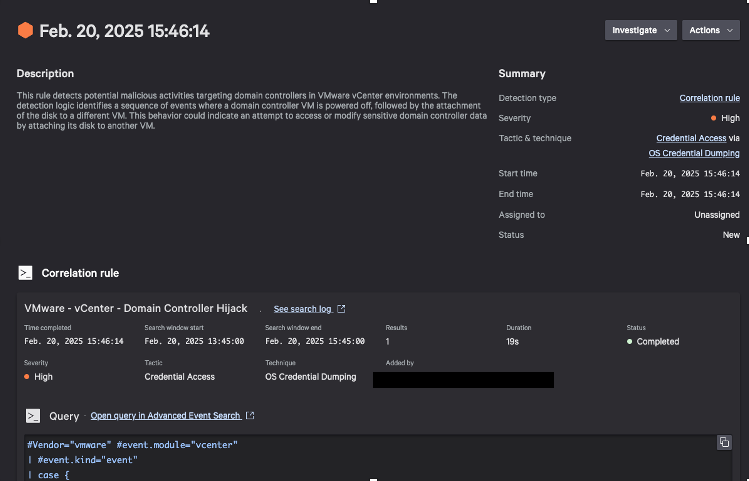
With elevated access to vCenter, adversaries will try not only to persist within the environment but also to achieve objectives such as credential access or data exfiltration against critical infrastructure. With more critical systems — such as Active Directory domain controllers (DCs), databases, file servers, and more — becoming virtualized, adversaries can target these sensitive systems through the VM virtual disks within their vCenter access.
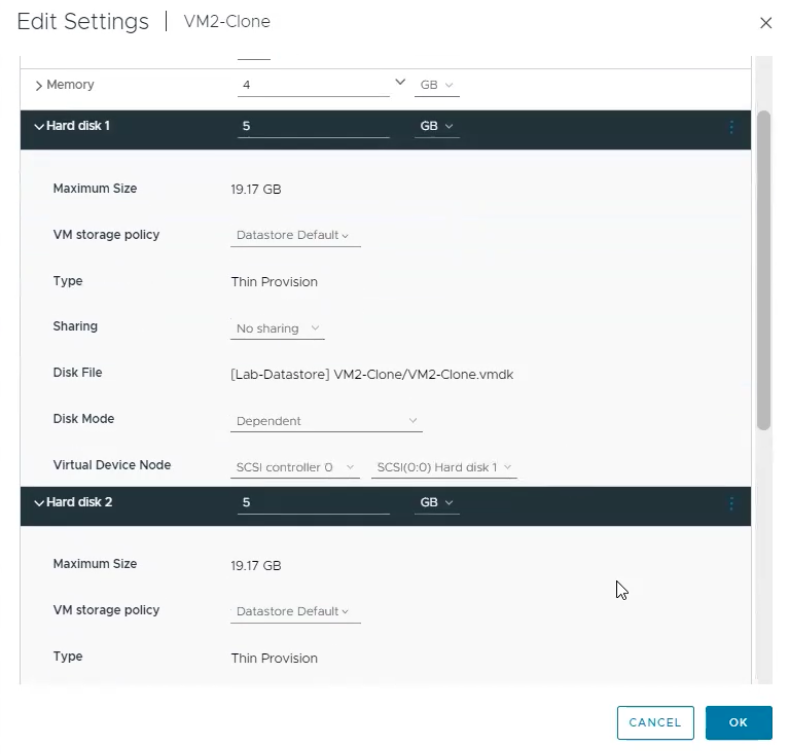
A common attack target is a DC's NTDS.dit database, containing the domain NTLM hashes and other sensitive data. To access the NTDS.dit of a virtual DC, adversaries will generally create a VM prior and use the VM to mount the virtual disk of the DC. The adversary could then use tools like Impacket to dump the credentials stored therein.
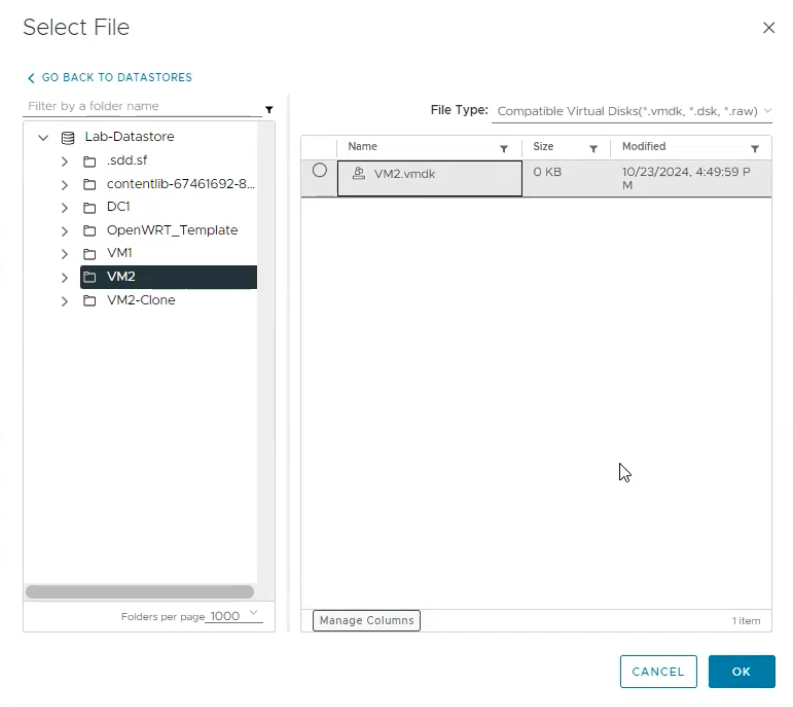
In order to create a VM, an adversary would likely have elevated access to vCenter. After this VM is created, the adversary could use the UI search functionality to find a virtual DC by looking for common naming schemes such as "DC." The adversary would subsequently shut down the target DC, then reconfigure their VM to attack the DC VMDK. With the attached VMDK, the adversary could use tools like secretsdump.py to dump the credentials from the DC.
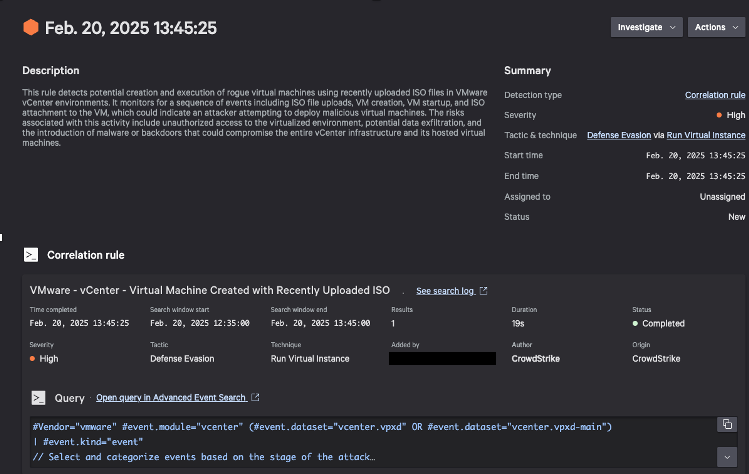
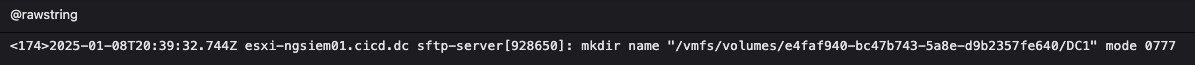
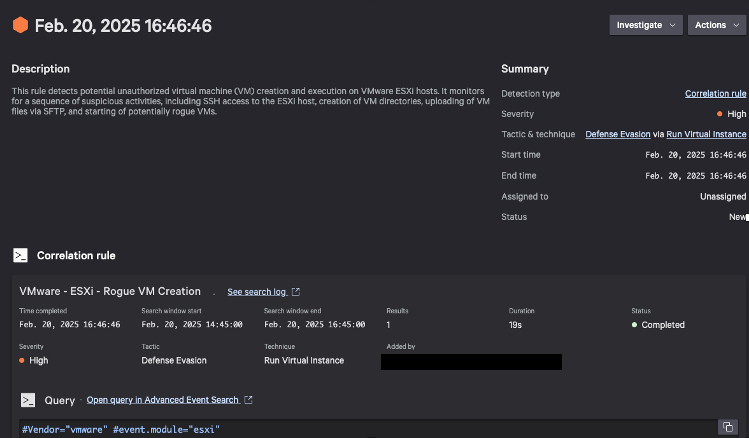
An example of these operations within a vCenter environment can be seen in Figures 7 and 8.