
VMware Explore 2025 Recap: VCF + Private AI + Broadcom Knights = Customer Focus
October 4, 2025
Bharti Airtel Announces a Strategic Partnership with IBM to Augment Airtel Cloud
October 16, 2025Cybersecurity Snapshot: Cybersecurity Awareness Month Arrives To Find AI Security a Hot Mess, as New OT Security Guidelines Highlight Architecture Mapping
Key takeaways
- Your staff is likely feeding sensitive data to AI tools you don’t know they’re using. Time to rev up your AI security awareness training.
- OT security teams must have a full understanding of their OT environment’s architecture in order to fully protect it.
- A new standard specification seeks to add consistency to the technical jargon used in post-quantum cryptography.
1 - It’s Cybersecurity Awareness Month, and the state of AI security ain’t good
Cybersecurity Awareness Month is here and boy, do we need a special focus on cyber right now, especially on the area of AI security.
How precarious is the AI security situation? Check out these stats:
- Everyone's using it: AI usage is booming, with 65% of people using AI tools, up from 44% a year ago.
- Most aren’t trained for it: A whopping 58% of employees have received zero training on AI security or privacy risks.
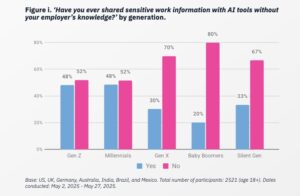
- Business secrets are spilling: 43% of employees admit to feeding company info into AI tools. We're talking internal documents (50%), financial data (42%) and even client data (44%).
Those numbers come from the report “Oh, Behave! The Annual Cybersecurity Attitudes and Behaviors Report 2025-2026” from the National Cybersecurity Alliance and CybSafe. Published this week, the report is based on a survey of 7,000-plus respondents from Australia, Brazil, Germany, India, Mexico, the U.K. and the U.S.
Screenshot
“The rapid rise in AI usage is the double-edged sword to end all double-edged swords: while it boosts productivity, it also opens up new and urgent security risks, particularly as employees share sensitive data without proper oversight,” reads the report.
And it’s not like people are clueless about AI risks. They’re worried about AI super-charging scams and cyber crime (63%), fake info (67%), security system bypassing (67%) and identity impersonation (65%). Yet, respondents’ faith in companies adopting AI responsibly and securely is only 45%.
As the gap between people’s AI adoption and AI security awareness widens, so does the attack surface security teams must protect. In fact, shadow AI, which is the unauthorized use of AI tools in the workplace, is “here to stay” and “becoming the new norm,” the report states, attributing its rise to insufficient AI security awareness training.
“Without urgent action to close this gap, millions are at risk of falling victim to AI-enabled scams, impersonation, and data breaches,” Lisa Plaggemier, Executive Director of the National Cybersecurity Alliance, said in a statement.
2 - Here's your Cybersecurity Awareness Month care package
The cyber industry has your back with a bunch of free resources this month. Here’s a quick roundup of some of them:
- National Cybersecurity Alliance: Along with their eye-opening report, the NCA is running a “Stay Safe Online” campaign, which includes the “Protecting Your Business’s Cash from Cyber Criminals” webinar on Oct. 28 at 1 pm ET.
- CISA: As part of its “Building a Cyber Strong America” campaign, the U.S. Cybersecurity and Infrastructure Security Agency is offering a cybersecurity awareness toolkit for organizations, as well as cyber guidance for small and medium-sized businesses (SMBs) and for state and local governments.
- SANS Institute: Worried about AI? SANS' “AI Awareness Toolkit” aims to help organizations educate their employees about AI cyber risks. It includes factsheets, a sample AI acceptable use policy, an infographic, tip sheets and more.
- World Economic Forum: Get the 30,000-foot view with WEF's article “Cybersecurity Awareness Month: 10 things to know in 2025,” which covers everything from the talent shortage to the threat of agentic AI.
- And of course, stay tuned to Tenable! As a partner of the NCA's Cybersecurity Awareness Month effort, we'll be raising awareness of simple, proven ways to boost online safety and sharing tips to put these cyber practices into action.
3 - Memo to OT teams: You can't secure what you can't see
If you’re tasked with securing your organization’s operational technology (OT) systems, this one’s for you.
This week, U.S. and U.K. cyber agencies published the guide “Creating and maintaining a definitive view of your OT architecture” with a simple message: you need a complete, up-to-date map of your OT systems and network.
“A definitive OT record enables organizations to conduct more comprehensive risk assessments, prioritize critical and exposed systems, and implement appropriate security controls,” CISA said in a statement.
The guidance also tackles third-party risk management, OT data security and architectural controls design.
Having the visibility that this “definitive OT record” provides is increasingly critical because OT networks are no longer isolated islands. They’re connected to IT networks and the internet, making them an attractive target.
This record should be your single source of truth for every OT component, connection and configuration. To properly assemble this OT architecture map, the guide, co-authored by the U.K.'s National Cyber Security Centre (NCSC), prescribes five core principles:
- Define your process: Figure out how you'll collect, validate and maintain information for this OT map.
- Lock it down: Establish an OT information-security management program to protect the confidentiality, integrity and availability of OT information.
- Know what matters: Identify and categorize your assets so you can protect the most critical ones first by making informed, risk-based decisions.
- Trace the wires: Identify and document every OT connection to build effective security controls.
- Monitor your suppliers: Understand and document the risks coming from third-party vendors that have access to your systems.
Following these steps will give you the visibility needed to defend your OT environment effectively, according to CISA and the NCSC.
4 - U.K. NCSC champions common post-quantum terminology
There’s a communication problem among those working on post-quantum cryptography (PQC), and the U.K.’s cyber agency wants to help solve it.
This week, the U.K. National Cyber Security Centre promoted a specification to standardize the terminology used by organizations developing and adopting cryptography that can withstand attacks powered by quantum computers.
“Consistent terminology across PQC ensures that technical proposals and discussions have clarity and consistency, and prevents misunderstandings that can lead to security issues,” reads an NCSC blog.
The new standard, which the NCSC developed along with Dr. Britta Hale from the Naval Postgraduate School, is named RFC 9794 and was published by the Internet Engineering Task Force (IETF) in June.
The new terminology is especially important for discussing "hybrid" scenarios in which traditional cryptography and PQC are used in tandem.
The goal of RFC 9794 is to ensure that everyone, from technical experts to policymakers, can communicate effectively and make informed decisions about securing systems against the quantum threat.
The new standard is already being adopted in technical drafts, academic papers and guidance from other standards bodies, demonstrating its immediate and significant impact on the cybersecurity field, according to the NCSC.
Quantum computers that can break today’s cryptographic algorithms are expected to be available at some point during the next decade.
5 - CIS updates Benchmarks for Google, Microsoft and Oracle products
Does your organization use the CIS Benchmarks to strengthen software configurations? The Center for Internet Security (CIS) just rolled out its monthly update of secure-configuration guidelines. It's time to check the list and harden your systems.
This month's updates include guidelines for Windows Server, Oracle Database, Google ChromeOS and many more.
Related Articles
When are attacks truly driven by AI?
February 25, 2026 0
Dell PowerEdge R770 Review A Fluid New 2U Server
February 18, 2026 0Scalar Tape Storage
February 15, 2026 0Why Certification Has Become a Strategic Control for CISOs
February 15, 2026 0


