
What Is RBAC? The Complete Guide to Role-Based Access Control
July 22, 2025
Accelerating America’s AI Advantage: Infrastructure, Workforce and Innovation
July 26, 2025
CrowdStrike Detects and Blocks Widespread SharePoint Zero-Day Exploitation
Learn more about this emerging threat and how CrowdStrike customers can use the Falcon platform to protect their environments.
Beginning on July 18, 2025, at approximately 0700 UTC, CrowdStrike Falcon® Complete Next-Gen MDR and CrowdStrike Falcon® Adversary OverWatch™ identified a wave of Microsoft SharePoint exploitation attempts by an unknown adversary. Two distinct zero-day vulnerabilities were made publicly available: a critical remote code execution vulnerability (CVE-2025-53770) and a server spoofing vulnerability (CVE-2025-53771). The chaining of these vulnerabilities to exploit a vulnerable SharePoint server is being referred to as “ToolShell.”
Since the start of this exploitation, CrowdStrike has observed and successfully blocked hundreds of exploitation attempts across 160+ customer environments, demonstrating both the scale of this threat and the effectiveness of our protection capabilities.
The CrowdStrike Falcon® platform detects and protects against exploitation of the Microsoft SharePoint zero-days, blocking known behaviors associated with these vulnerabilities. This blog post provides context surrounding this emerging threat, as well as guidance for customers on how they can use the Falcon platform to protect their environments. Customers of CrowdStrike Falcon® Adversary Intelligence can find more detailed analysis in Intel report CSA-250846.
Observed Exploitation of SharePoint Vulnerability
CrowdStrike has observed widespread exploitation of CVE-2025-53770 involving a deserialisation attack leading to attempts to write a malicious .aspx webshell on the host. That file, spinstall0.aspx, is used to steal IIS Machine Keys, which can later be used for other post-exploitation attacks.
This attack begins with a specially crafted POST request to an accessible SharePoint server. The POST request payload will attempt to write the .aspx file via PowerShell. That malicious PowerShell command, spawned from the SharePoint IIS process, is blocked by the Falcon platform.
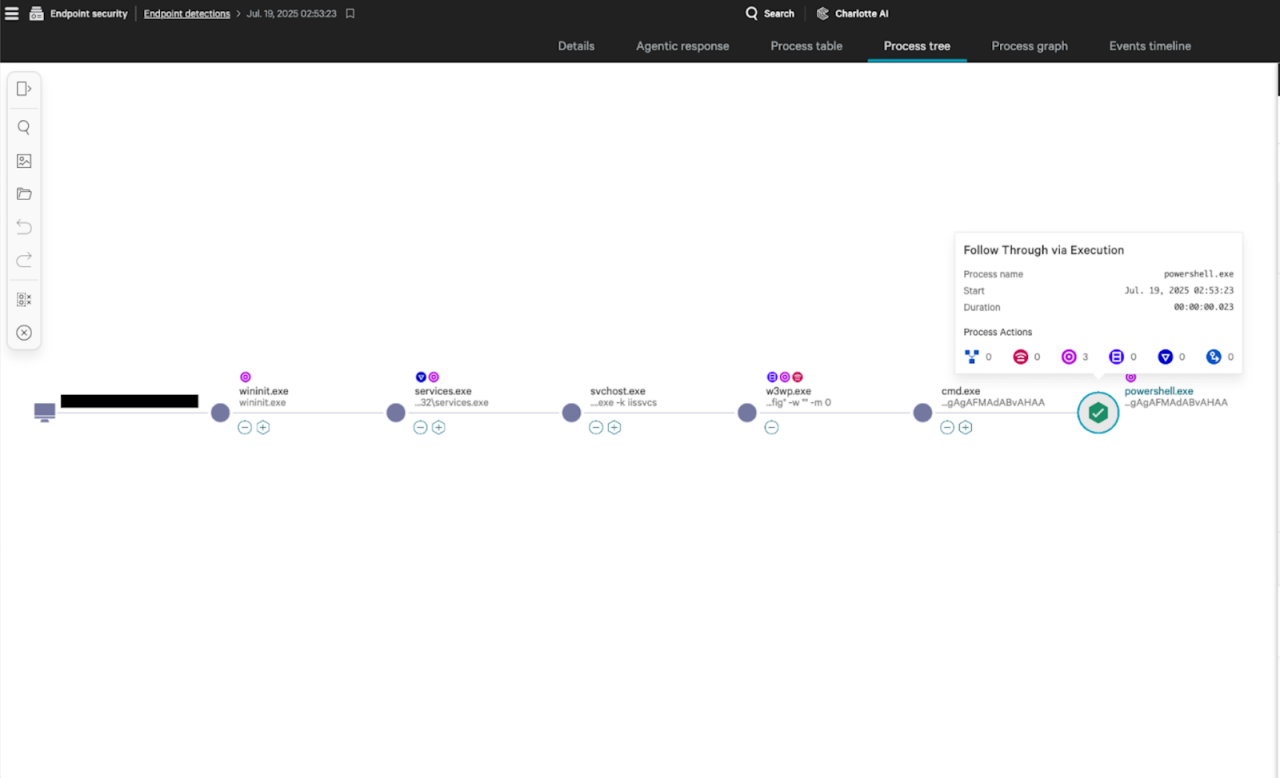
Figure 1. Blocked PowerShell spawned from the SharePoint worker process w3wp.exe (click to open in new tab)
We have tracked the size and speed of attempted payload delivery over time by mapping detections from the Falcon platform. The following timeline of activity has been observed:
- July 18 (morning UTC): A small number of SharePoint servers were attacked
- July 18 (1330-1845 UTC): Shortly after, likely following the publicity of the zero-day, the campaign ramped up significantly with 177 servers attacked on the same day
- July 19 (0600-0800 UTC): Exploitation recommenced briefly before temporarily ceasing
- July 21 (0740 UTC): Activity resumes with 32 servers attacked in four hours up to 1130 UTC
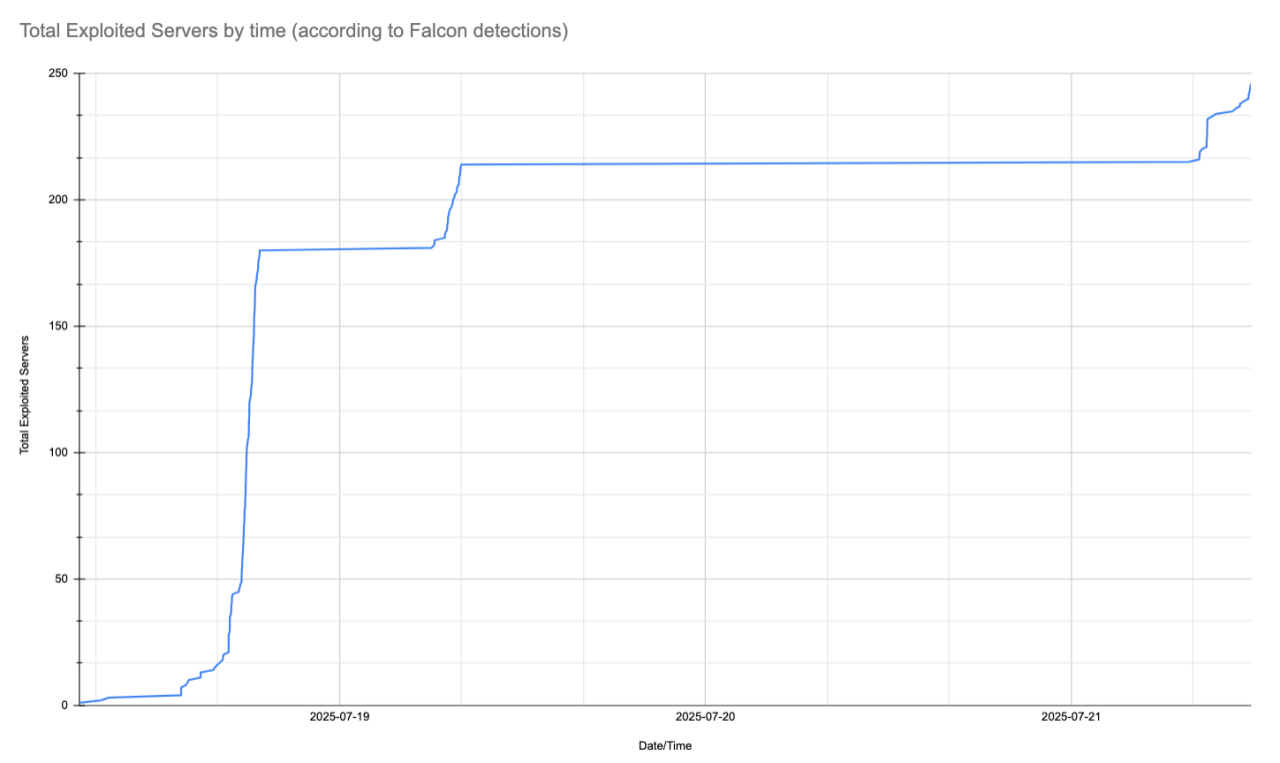
Figure 2. Observed instances of attempted exploitation of SharePoint servers over time (click to open in new tab)
Defending Against This Threat
Organizations are strongly encouraged to apply patches that have been released to ensure they are protected. At the time of writing, patches for Microsoft SharePoint Server 2019 Core and Microsoft SharePoint Server Subscription Edition are currently available. Patches for Microsoft SharePoint Enterprise Server 2016 were still being actively tested by Microsoft.
CrowdStrike Falcon Endpoint Detection and Response
As mentioned in our opening analysis, this attack relies on specially crafted POST requests to exploit the SharePoint zero-day vulnerabilities. CrowdStrike Falcon® Insight XDR endpoint security successfully detected and blocked these attacks through advanced behavioral analysis rather than relying on signature-based detections.
The attack chain exploits SharePoint servers by executing malicious code to extract authentication keys, enabling attackers to send authenticated system-level commands. Falcon Insight XDR’s behavioral engine identified suspicious activity when SharePoint processes began launching command prompts and PowerShell scripts — a clear deviation from normal SharePoint operations.
Our multi-layered approach detected:
- Abnormal process behavior: Suspicious process chains originating from SharePoint services, including webshells and reconnaissance
- Network anomalies: Questionable DNS requests that generated alerts in the Falcon console
- Behavioral correlation: Multiple indicators confirming malicious intent
Threat actors continuously adapt their techniques based on security vendor responses. CrowdStrike's threat research team proactively enhances our detection capabilities in response. We are deploying additional behavioral detections this week that focus on post-exploitation activities and alternative attack vectors, providing continued coverage as attack methods evolve.
CrowdStrike Falcon Exposure Management
Customers can find CVE-2025-53770 and CVE-2025-53771 with CrowdStrike Falcon® Exposure Management’s vulnerability management capability.
Falcon Exposure Management has had detections for all supported platforms since the vulnerability was initially disclosed. The vulnerability currently has an ExPRT.AI severity rating of "Critical," with an exploit status of "Actively Used (Critical)" due to confirmed active exploitation in the wild.
To identify vulnerable systems, customers can navigate to the Exposure Management > Vulnerability Management > Vulnerabilities page in the CrowdStrike Falcon platform. From there, they can use the Vulnerability ID filter with a value of "CVE-2025-53770" and/or “CVE-2025-53771.” If any of the managed systems are vulnerable, results will be shown here. If they receive the message "No vulnerabilities found," then all of their managed SharePoint systems have the necessary patches. For any systems found vulnerable, the remediation guidance provided for that system will mention the necessary security updates to apply.
CrowdStrike Falcon Next-Gen SIEM
As the vulnerabilities discussed target the SharePoint server, ingestion of Microsoft IIS server logs provides a comprehensive view into this emerging threat. CrowdStrike Falcon® Next-Gen SIEM customers are encouraged to ingest IIS logs to gain the necessary visibility and detect malicious actions. Further information about ingesting and parsing this data source is available to customers here. The “Microsoft - IIS - Microsoft Sharepoint ToolShell Exploitation CVE-2025-53770” rule template is currently available to customers who wish to detect possible exploitation attempts specific to CVE-2025-53770. This template leverages the following query to identify instances where malicious URLs are being accessed:
#Vendor="microsoft" #event.module="iis" #event.dataset="iis.access" #repo!="xdr*" | http.request.method="POST" url.path="/_layouts/15/ToolPane.aspx" url.query="DisplayMode=Edit&a=/ToolPane.aspx" http.request.referrer="/_layouts/SignOut.aspx" | http.response.status_code =~ in(values=[200,302])
Falcon Next-Gen SIEM users may also leverage a hunting query that uses the recently released correlate() capability. This rule, which is also provided below, may be used to identify instances where a SharePoint IIS process results in a PowerShell command being executed, followed by an ASPX file being written.
correlate(
cmd: {
#event_simpleName=ProcessRollup2 event_platform=Win FileName="cmd.exe" ParentBaseFileName="w3wp.exe"
} include: [aid, ComputerName, TargetProcessId, ParentBaseFileName, FileName, CommandLine],
pwsh: {
#event_simpleName=ProcessRollup2 event_platform=Win FileName="powershell.exe"
| aid <=> cmd.aid
| ParentProcessId <=> cmd.TargetProcessId
} include: [aid, ComputerName, TargetProcessId, ParentBaseFileName, FileName, CommandLine],
aspx: {
#event_simpleName=/^(NewScriptWritten|WebScriptFileWritten)$/ event_platform=Win FileName=/\.aspx/i
| aid <=> cmd.aid
| ContextProcessId <=> pwsh.TargetProcessId
} include: [aid, ComputerName, TargetBaseFileName],
sequence=true, within=5m)
Conclusion
The SharePoint vulnerability exploitation demonstrates how critical application threats can provide attackers with initial access to organizations. CrowdStrike customers benefit from multiple layers of protection against these attacks.
While we strongly recommend patching SharePoint instances immediately, the Falcon platform provides comprehensive protection through:
- Falcon Insight XDR: Behavioral detection and prevention of exploitation attempts
- Falcon Exposure Management: Visibility into vulnerable SharePoint instances
- Falcon Next-Gen SIEM: Detection rules for Microsoft IIS logs to identify exploitation attempts
CrowdStrike will continue monitoring this threat and update our guidance as new information emerges.
Source
Related Posts
When are attacks truly driven by AI?
February 25, 2026 0
Dell PowerEdge R770 Review A Fluid New 2U Server
February 18, 2026 0Scalar Tape Storage
February 15, 2026 0Why Certification Has Become a Strategic Control for CISOs
February 15, 2026 0Powering A New Era of Confidential AI With Confidential Computing
February 15, 2026 0



